Key Highlights
- Australian researchers developed an algorithm with a 99% success rate in intercepting man-in-the-middle cyberattacks on military robots.
- The deep learning-based intrusion detection framework promises robust cybersecurity for highly networked robot operating systems, addressing vulnerabilities in the age of Industry 4.0.
Australian researchers have developed an innovative algorithm capable of swiftly intercepting and halting man-in-the-middle (MitM) cyberattacks on unmanned military robots. This groundbreaking development has the potential to bolster the security of autonomous systems in critical military applications.
Simulating Human Brain Behavior for MitM Cyberattack Detection
Researchers from Charles Sturt University and the University of South Australia (UniSA) collaborated to create this algorithm, employing deep-learning neural networks to simulate human brain behavior.
- The primary objective was to teach the robot’s operating system to recognize the telltale signs of a MitM eavesdropping cyberattack, a scenario where attackers infiltrate ongoing communications or data transfers.
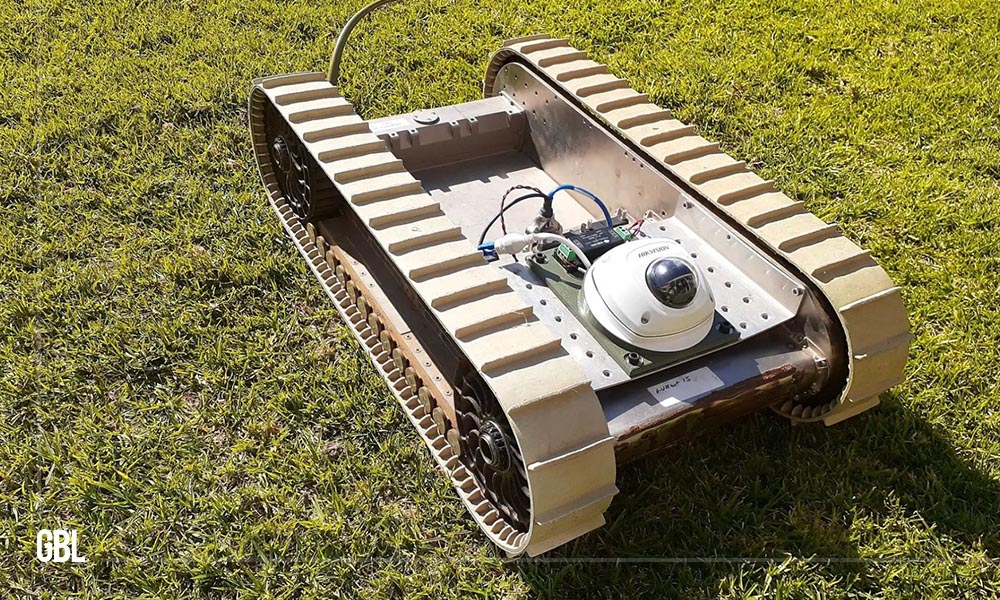
- The algorithm was put to the test in real-time using a replica of a United States Army combat ground vehicle.
- The results were impressive, with a success rate of 99% in preventing malicious attacks and an extraordinarily low false positive rate of under 2%, confirming its effectiveness.
- This research has been documented in IEEE Transactions on Dependable and Secure Computing.
Advancing Cybersecurity for Robot Operating Systems
Professor Anthony Finn, a researcher in autonomous systems at UniSA, emphasized that this algorithm surpasses existing cyberattack recognition techniques. The vulnerability of robot operating systems (ROS) to data breaches and electronic hijacking is a considerable concern due to their extensive networking in highly collaborative environments, a hallmark of Industry 4.0 that combines robotics, automation, and the Internet of Things.
- The researchers are optimistic about the future because of the rapid advancements in computing capabilities, which enable the development and implementation of sophisticated AI algorithms to safeguard systems against digital threats.
- Dr. Fendy Santoso, from Charles Sturt’s Artificial Intelligence and Cyber Futures Institute, noted that despite its widespread use, the robot operating system often overlooks security issues in its coding.
- This oversight arises from the encryption of network traffic data and limited integrity-checking capabilities.
Leveraging the Power of Deep Learning for Intrusion Detection
Dr. Santoso highlighted the strength of their intrusion detection framework, underpinned by deep learning, describing it as robust and highly accurate. The system is designed to manage large datasets effectively, making it suitable for protecting large-scale and real-time data-driven systems like ROS.
Looking ahead, Professor Finn and Dr. Santoso plan to subject their intrusion detection algorithm to further testing on various robotic platforms, including drones. These platforms possess faster and more complex dynamics compared to ground-based robots, making the algorithm’s adaptability a crucial factor in securing a wide range of autonomous systems.
FAQs
1. What is the purpose of the developed new cyber algorithm?
The algorithm is designed to intercept and halt man-in-the-middle (MitM) cyberattacks on unmanned military robots.
2. What techniques were used to develop new cyber algorithm?
The researchers employed deep learning neural networks to simulate human brain behavior, training the robot’s operating system to recognize MitM cyberattacks.
3. How successful is the algorithm in preventing cyberattacks?
The algorithm achieved an impressive 99% success rate in preventing malicious cyberattacks with a false positive rate of less than 2%.
4. Why are robot operating systems (ROS) vulnerable to cyberattacks?
ROS systems are highly networked, making them susceptible to data breaches and electronic hijacking, which is a concern in the context of Industry 4.0.